There have been many reports in 2016 of devastating malware, but the most recent, called Locky, could be the scariest yet. It may have a silly name, but it is a seriously threatening ransomware. Like similar ransomware viruses we have seen, this one is received in the form of an email with an attached “invoice” that is a Microsoft Word file. The attachment contains malicious macros and has infected computers and networks all over the world. Antivirus engines are working to update and catch it, but it is still spreading quickly.
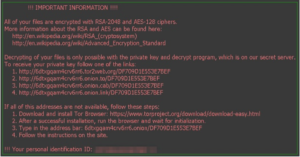 The email contains a heading with a subject line calling attention to an invoice number. If you click on the attachment, the macros will download the Locky ransomware that will encrypt all of the files on your computer and network. It also changes the filenames for encrypted files to make it difficult to restore data. In addition, this ransomware encrypts network based backup files. Once encrypted, victims receive a message on their computer screens instructing them to go to the attackers’ website for payment.
The email contains a heading with a subject line calling attention to an invoice number. If you click on the attachment, the macros will download the Locky ransomware that will encrypt all of the files on your computer and network. It also changes the filenames for encrypted files to make it difficult to restore data. In addition, this ransomware encrypts network based backup files. Once encrypted, victims receive a message on their computer screens instructing them to go to the attackers’ website for payment.
Without offsite backup storage, the prospect of restoring data is bleak. As we have advised in other posts about ransomware, the best means of prevention is education and a disaster contingency plan. Educate ALL of your employees on the dangers of clicking attachments in emails from unknown sites. Ensure that you have a disasater recovery plan in place and work closely with your IT professionals, keeping updated on new information. The only backup plan that will prevent lost data and disaster is to have both onsite and offsite backup storage to recover in event of a local appliance becoming corrupted. A good disaster recovery package (BDR) will do this.
This post hits close to home, since one of our clients was infected with the ransomware as we were preparing the article. Fortunately, they had chosen a good BDR package, which included an offsite backup. Working closely with us, they were back up within hours.
A recent article from zdnet.com noted that “action on economic crime is not the responsibility of one person or team, it must be embedded in an organisation’s culture.” Keep in contact with your IT professionals and work with them to ensure your organization is cyber crime savvy.